ClickFix Malware Now Abuses Nslookup to Deliver Remote RATs
Executive Summary
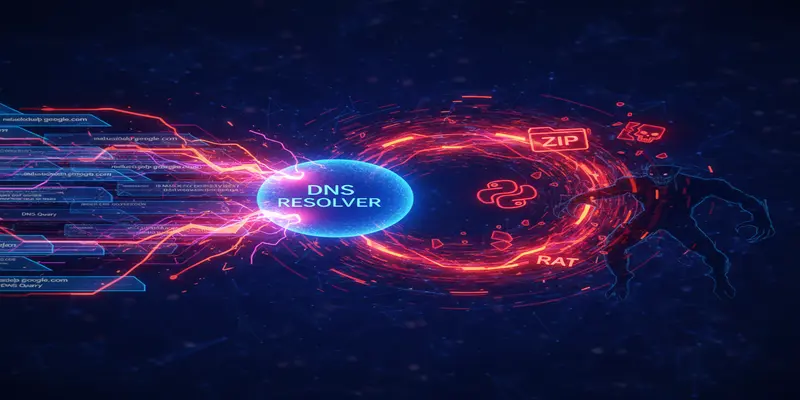
ClickFix, a well-known malware distribution campaign, has evolved by weaponizing the nslookup utility to download payloads and circumvent modern detection mechanisms. This marks a shift in attacker tradecraft where DNS queries—typically benign—are now vectors for multi-stage malware deployment. This threat intelligence report examines how ClickFix retools outdated utilities to spread ModeloRAT, a potent Python-based remote access trojan (RAT), and highlights urgent takeaways for defender teams.
What Happened
Recent analyses reveal that ClickFix campaigns have moved away from previously used PowerShell and mshta scripts—both increasingly mitigated by security software—and have instead adopted a more deceptive approach leveraging nslookup. The attack flow begins innocuously: users are presented with fake CAPTCHA prompts, fake system warnings, or bogus support instructions. Victims are tricked into copying a command that, when run on Windows or macOS, uses the seemingly harmless nslookup command to query a DNS server.
However, instead of merely resolving domain names, the DNS server responds with specially crafted text fragments that, when interpreted by the command line, further the infection chain. This chain involves downloading a ZIP archive that houses a malicious Python script. Once executed, this script performs reconnaissance, executes local system discovery, and drops Visual Basic Scripts designed to install ModeloRAT on the machine.
ModeloRAT gives full remote access to attackers and allows post-compromise operations, including surveillance, lateral movement, and persistence.
Why This Matters for CISOs
Organizations should be alarmed by this campaign—not just because it delivers a capable RAT, but because it leverages overlooked tooling for initial infection. Enterprises relying on PowerShell and script monitoring for detection will find nslookup-based exploits slipping past traditional defenses.
This technique impacts governance layers around endpoint command execution, script control policies, and user education. For security teams, this emphasizes the need for improved behavioral detection—not just static command blacklists.
For CISOs in environments where DNS monitoring is subpar or deprecated tools are assumed safe, responding to this tactic is essential to maintaining enterprise ransomware defense posture.
Threat & Risk Analysis
Attack Vectors:
ClickFix exploits user trust and operating system utilities. Attackers trick users into self-infecting by mimicking support help desks or security prompts. When users copy-paste the attacker-supplied command, nslookup retrieves DNS responses containing embedded malicious code or pointers to ZIP payloads.
Exposure Scenarios:
- Home and enterprise users executing fake "diagnostic" commands
- Teams using DNS without robust monitoring or filtering
- Devices with Python pre-installed (common in engineering or development environments)
- Users with elevated privileges unknowingly initiating downloads
Supply Chain Relevance:
While this campaign currently targets end users, its use of DNS-based command delivery highlights DNS infrastructure as an emerging threat vector in the broader supply chain. A compromised recursive resolver or misconfigured internal domain could lead to similar abuses internally.
Attacker Motivations:
This campaign showcases a common objective: evasion. By rerouting delivery mechanisms through nslookup, attackers bypass traditional security engines trained to flag PowerShell and mshta activity. It's a targeted advancement in payload smuggling for long-term access.
Potential Enterprise Impact:
- Compromise of endpoint devices with remote access capability
- Data exfiltration and reconnaissance leading to further attacks
- Reduced visibility due to trusted utility exploitation
- Risks to development or OT environments where legacy tools are still live
For context, attacks like this underscore the value of integrated daily cyber threat briefings and defensive insight into overlooked tools.
MITRE ATT&CK Mapping
-
T1059.003 — Command and Scripting Interpreter: Windows Command Shell
The attacker executes text commands via the Run dialog/terminal. -
T1071.004 — Application Layer Protocol: DNS
DNS is repurposed to fetch encoded data or commands. -
T1027 — Obfuscated Files or Information
Payloads are disguised via DNS replies to evade analysis. -
T1055 — Process Injection
Final payloads like ModeloRAT can use injection for stealth. -
T1012 — Query Registry
Used during reconnaissance phase post-infection. -
T1566.002 — Phishing: Fake technical support
Victims are deceived through websites imitating support services.
Key Implications for Enterprise Security
- Traditional script-blocking isn’t enough—command behavior matters more than syntax.
- Legacy tools like nslookup must now be included in threat modeling.
- DNS responses can no longer be blindly trusted on endpoints.
- User training must include awareness of “copy this command to fix” scams.
- EDR solutions need context-aware detection for indirect post-exploitation steps.
Recommended Defenses & Actions
Immediate (0–24h)
- Deploy detections for suspicious
nslookupusage in EDR/XDR platforms - Block outbound DNS queries to unknown or untrusted domains
- Alert on clipboard activity tied to command-line interactions
Short Term (1–7 days)
- Conduct threat hunting for systems that accessed attacker-supplied DNS servers
- Educate helpdesk and support teams on new ClickFix delivery methods
- Review endpoint policies to disallow use of built-in tools like nslookup from non-admin users
Strategic (30 days)
- Incorporate behavior detection rules for legacy utilities into SIEM workflows
- Update user training materials to reflect evolving social engineering payloads
- Implement comprehensive patch management strategy inclusive of command-line monitoring tools
Conclusion
ClickFix’s shift to nslookup weaponization is a reminder that even trusted administrative tools can become delivery vectors with the right manipulation. As attackers innovate and adapt, defenders must mature beyond static blocklists and reactive policies. Detecting behavior—rather than syntax—is now critical. For CISO teams focused on enterprise resilience, this cybersecurity report reinforces the urgency of re-evaluating endpoint command usage policies and DNS activity monitoring.
Start Your 14-Day Free Trial
Get curated cyber intelligence delivered to your inbox every morning at 6 AM. No credit card required.
Get Started Free

