Malwarebytes Highlights January’s Emergent Threat Landscape
Executive Summary
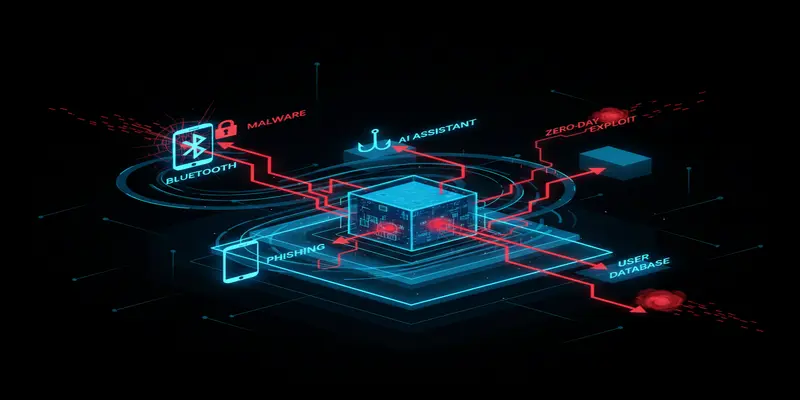
The Malwarebytes Labs threat roundup from January 12–18 reveals a volatile and multifaceted threat intelligence report for CISOs navigating 2026’s early cybersecurity headwinds. Insights span novel hardware exploits, deceptive phishing campaigns, and stealth malware tactics—underscoring the wide scope of enterprise risks requiring vigilance.
What Happened
Malwarebytes Labs reported a packed week of adversarial activity. Key incidents include:
- WhisperPair, a Bluetooth-based vulnerability, exposes users of wireless earbuds and headphones to real-time eavesdropping and location tracking.
- Dutch police conducted a cyber deception campaign by selling fake concert tickets, aiming to educate users on social engineering and digital awareness.
- Attackers leveraged a newly identified "Reprompt" exploit to harvest sensitive data from Microsoft Copilot, exploiting its reauthentication prompts.
- LinkedIn became a vector for phishing, with attackers posting fraudulent “account restricted” warnings to trick professionals into sharing credentials.
- Digital skimming via Magecart was discovered targeting major online retailers by compromising third-party payment networks.
- Seemingly legitimate software downloads were observed acting as delivery vectors for stealthy remote access backdoors.
- A data broker was fined for selling medical data, including patient details of Alzheimer’s sufferers, highlighting data privacy risks in commercial data pipelines.
- Apple urged all iPhone users to update and restart their devices, in response to yet-unconfirmed security concerns likely tied to system vulnerabilities.
- Regulators are scrutinizing AI-driven tool Grok amid its involvement with sexually explicit deepfake content generation.
These events present not only a technical challenge but also a governance and reputational risk that CISOs must address proactively across their digital environments.
Why This Matters for CISOs
The scope of attack surfaces—from AI platforms like Copilot to wireless peripherals—should prompt security leaders to assess the full spectrum of enterprise exposure and user behavior vulnerabilities. In particular, the crossover of physical-layer exploits (Bluetooth vulnerabilities), deceptive enterprise software integrations (Copilot reprompting), and e-commerce skimming points to a cloud security threats convergence that widens the attack aperture.
These developments expose weakly segmented device ecosystems, introduce accelerated legal scrutiny on data brokers and platforms, and highlight the growing risk of AI platform abuse within regulated business environments.
Threat & Risk Analysis
The week’s indicators of compromise encompass diverse attack vectors and motivations:
- Bluetooth Device Exploitation (WhisperPair): Attackers can hijack device-pairing signals undetected, enabling them to locate users or eavesdrop via exposed audio channels. While consumer-focused, these tactics could pivot quickly into enterprise contexts through bring-your-own-device (BYOD) policies.
- Phishing on Enterprise Platforms (LinkedIn): Posting fake “account restricted” messages exploits professional trust on corporate networking platforms. These campaigns sidestep traditional email gateways and are less detectable via enterprise spam filters.
- Software Supply Chain Poisoning: Malware-laced software downloads pose a significant supply chain threat, especially when delivery vectors impersonate legitimate IT tools or developer utilities. This is exacerbated in decentralized or under-monitored environments.
- Magecart Skimming: Known for JavaScript injection attacks on checkout pages, Magecart actors now breach third-party payment service providers, making identification and containment far more difficult.
- Data Broker Accountability: Regulatory fines for selling patient data reveal significant third-party compliance risks. Enterprises must scrutinize contractual data flows, especially when sensitive PII or health data is involved.
- AI Assistant Abuse (Copilot "Reprompt" Attack): Threat actors exploit the ambient authentication interfaces of AI copilots, forcing users to reauthenticate into sessions attackers can intercept—compromising session integrity and internal data visibility.
These scenarios reinforce the need for both real-time monitoring and human-driven analysis—strategies detailed in our daily cyber threat briefings and comprehensive patch management strategy for proactive risk containment.
MITRE ATT&CK Mapping
- T1086 — PowerShell: Remote malware downloads were executed via obfuscated PowerShell scripts bundled with “safe” installers.
- T1203 — Exploitation for Client Execution: The Copilot Reprompt issue exemplifies attackers triggering unauthorized code execution via manipulated UI flows.
- T1071.001 — Application Layer Protocol: Web Protocols: Magecart skimming exploits web JavaScript payloads to transmit sensitive data.
- T1566.002 — Spearphishing Link: Fake comments on LinkedIn redirect victims to phishing sites masked as legitimate account portals.
- T1557 — Man-in-the-Middle: WhisperPair-style Bluetooth abuse permits interception of communication over wireless without authentication.
- T1021.001 — Remote Desktop Protocol: Once initial access is gained via trojanized installers, RDP channels appear used for lateral movement.
Key Implications for Enterprise Security
- Employees using unmanaged wireless accessories may expose enterprise environments to proximity-based tracking or audio surveillance.
- AI integration within productivity suites must undergo security reviews, including session handling and reauthentication routines.
- Enterprise phishing protection must now include social platforms like LinkedIn, not just traditional inbox monitoring.
- Magecart campaigns show renewed interest in compromising broad-scale financial data via supply-chain insertion.
- Regulatory risk is escalating—particularly around data brokers and AI tools distributing or generating harmful content.
Recommended Defenses & Actions
Immediate (0–24h)
- Perform urgent update cycles for all iOS devices.
- Audit third-party browser extensions, user-installed software, and recent downloads.
- Notify users about phishing campaigns on LinkedIn and mobile push channels.
Short Term (1–7 days)
- Deploy EDR rules to flag anomalous reauthentication activity in Copilot or other AI integrations.
- Ensure endpoint protection monitors for unusual Bluetooth proximity activity.
- Review app permissions and configuration of enterprise Bluetooth policies under mobile device management (MDM).
- Update web firewalls and DLP systems to hunt for Magecart markers and JavaScript injects.
Strategic (30 days)
- Introduce full lifecycle risk management for AI assistants integrated into M365, Google Workspace, or Copilot.
- Draft governance policies for acceptable device usage (including wireless wearables) on corporate networks.
- Formalize procedures for reviewing and auditing third-party vendor compliance with sensitive data laws.
- Establish red-team scenarios testing lateral movement via utility downloads or fake installers seeded through IT portals.
Conclusion
From wireless vulnerabilities to phishing traps lodged within professional networks, this week’s developments highlight the evolving boundaries of trust and misconfiguration. For security leaders, these trends define a cybersecurity report worth dissecting deeply—not just to detect intrusions, but to forecast adversarial targeting and shape adaptable defenses that outpace increasingly creative threat actors.
Start Your 14-Day Free Trial
Get curated cyber intelligence delivered to your inbox every morning at 6 AM. No credit card required.
Get Started Free

