Why CISOs Should Watch the Rise of AI-Powered Smart Cameras
Executive Summary
The convergence of artificial intelligence, local video analytics, and edge processing in smart home devices has created a new intersection between privacy, surveillance, and enterprise risk. This threat intelligence report examines the rise of AI-enhanced home security cameras like the EufyCam S3 Pro, which now offer 4K ultra-HD video, night vision in full color, facial recognition, and anomaly detection — all without a cloud backend. As this consumer-grade tech evolves, CISOs face growing questions around unauthorized surveillance, edge data collection, and potential misuse inside corporate or hybrid environments.
What Happened
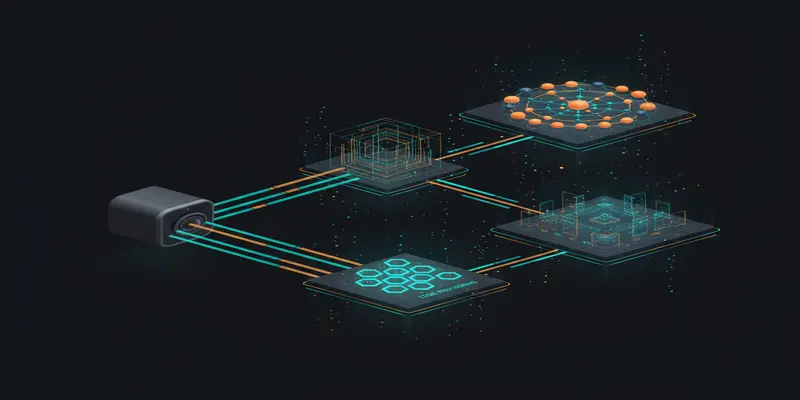
Anker’s latest model in its EufyCam line, the S3 Pro, debuted at CES 2026 and made headlines due to its combination of AI-enhanced imaging, superior night vision, and completely subscription-free architecture. The S3 Pro offers ultra-clear 4K resolution, real-time color night vision powered by an f/1.0 aperture and 1/1.8” sensor, and AI-driven edge analytics for facial, human, pet, and vehicle detection.
Unlike traditional cloud-integrated security ecosystems like Ring or Nest, Eufy’s cameras offer fully local storage via its HomeBase 3 hub. With improved SolarPlus 2.0 charging and low false alert rates due to dual motion detection, the device has shaped up to be a leader in the prosumer surveillance segment.
Notably, while Apple HomeKit Secure Video offers encryption, it forcibly downgrades video quality to 1080p and requires iCloud storage. Many users opt instead for Eufy’s privacy-forward local model to retain full 4K with zero cloud dependency.
Why This Matters for CISOs
With remote work redefined as a permanent fixture of workplace models, employee use of smart devices around sensitive environments is increasing. AI surveillance features embedded in consumer IoT devices like EufyCam S3 Pro pose serious challenges in terms of data governance, inadvertent exposure, and legal implications, especially in locations where regulated data is being handled.
Consumer-grade cameras now offer capabilities — such as local facial recognition, behavioral alerting, and edge-based anomaly processing — that previously required enterprise-grade surveillance software. This elevates the governance and oversight challenge for CISOs and legal teams, especially when these devices are used in home offices or hybrid workspaces.
These challenges align to emerging issues in cloud security threats, where data residency, accessibility, and third-party processing raise new operational and legal risks.
Threat & Risk Analysis
The EufyCam S3 Pro represents a new class of multifunctional edge surveillance that bypasses traditional cloud attack vectors, yet introduces its own form of privacy and data risks. Technical implications to consider:
- Attack Vectors: On-device processing reduces cloud exposure, but firmware vulnerabilities or insecure local APIs open pathways for unauthorized access or takeover.
- Exposure Scenarios: Cameras used in home offices may inadvertently record sensitive discussions, monitor unauthorized personnel, or capture screens and credentials.
- Supply Chain Relevance: Eufy, a subsidiary of Anker based in China, raises accountability concerns around firmware integrity and OTA updates. Firmware signing practices, update validation, and component sourcing must be scrutinized.
- Attacker Motivations: APT actors and cybercriminals may leverage edge devices for passive surveillance, internal recon, or physical intrusion reconnaissance. If connected to mobile devices or smart assistants, lateral escalation becomes plausible.
- Enterprise Impact: Data protection norms such as GDPR or CCPA may be violated unknowingly by employees installing surveillance devices that collect or process PII without proper disclosures.
As visibility into smart device behavior remains low, incorporating high-risk IoT into workspaces without formal vetting increases lateral risk. Regular reviews of approved device lists and AI-processing policies should be part of strong daily cyber threat briefings.
MITRE ATT&CK Mapping
-
T1471 — Data from Information Repositories
Cameras may inadvertently capture credentials on screens or verbalized authentication phrases. -
T1203 — Exploitation for Client Execution
Vulnerabilities in embedded camera software or its mobile app could enable remote compromise. -
T1027 — Obfuscated Files or Information
Malicious firmware modifications for data capture or backdoor access could be disguised during OTA updates. -
T1133 — External Remote Services
If internet-connected, the hub may open exposure to unwanted remote commands or surveillance. -
T1562 — Impair Defenses
Some attackers may disable local logging or alerting through compromised admin access or app exploits.
Key Implications for Enterprise Security
- Smart consumer surveillance is now enterprise-adjacent — and too capable to ignore.
- BYOD policies must evolve to account for edge AI devices, not just mobile phones and laptops.
- Unmonitored physical surveillance at home workspaces creates compliance and ethics risks.
- Data residency rules are challenged by on-device video archives with facial identification labels.
Recommended Defenses & Actions
Immediate (0–24h)
- Audit smart device policies for remote and hybrid employees; flag unsupported camera use.
- Conduct inventory scans for unapproved IoT endpoints in VPN or remote authenticated sessions.
Short Term (1–7 days)
- Update acceptable use policies to explicitly restrict auto-surveillance devices during work hours.
- Launch employee awareness campaigns on risks of smart camera placement near regulated work surfaces.
Strategic (30 days)
- Incorporate edge AI risk reviews into enterprise IoT governance frameworks.
- Partner with legal to assess privacy liability and employee consent models when facial recognition is used.
- Explore EDR/XDR integrations that can detect new telemetry from associated mobile camera apps or firmware pings.
Conclusion
The line between consumer convenience and corporate exposure is eroding. Surveillance-grade AI cameras like the EufyCam S3 Pro now operate in personal environments with the power and insight of enterprise security platforms. This cybersecurity report underscores the obligation of security leaders to understand — and proactively manage — this new hybrid frontier of physical and digital risk.
Start Your 14-Day Free Trial
Get curated cyber intelligence delivered to your inbox every morning at 6 AM. No credit card required.
Get Started Free

