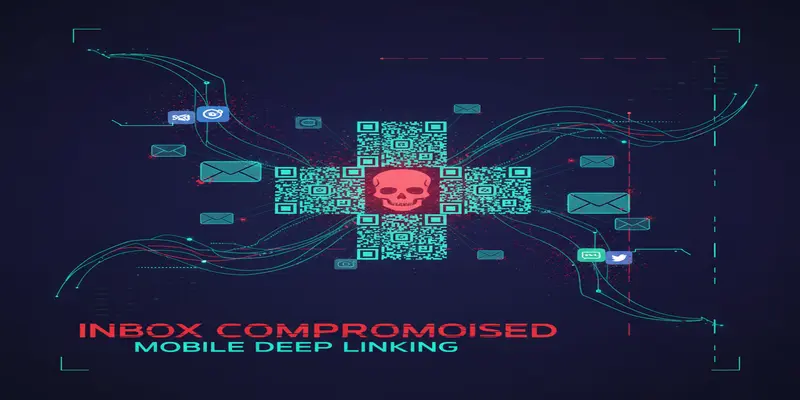
CrowdStrike FalconID Enhances Phishing-Resistant MFA for CISOs
CrowdStrike's FalconID introduces advanced phishing-resistant multi-factor authentication integrated into its Falcon platform, empowering CISOs to counter increasingly sophisticated identity threats.