
Emerging Threat: VoidLink Framework Enables Modular Linux Malware
VoidLink, a modular Linux malware framework, is being used by UAT-9921. CISOs should assess visibility and controls around cloud and hybrid Linux-based assets.
Security vulnerabilities remain the most common entry point for cyber attacks. This section tracks newly discovered CVEs, zero-day vulnerabilities, and actively exploited flaws affecting enterprise infrastructure, cloud environments, and software supply chains.
63 articles

VoidLink, a modular Linux malware framework, is being used by UAT-9921. CISOs should assess visibility and controls around cloud and hybrid Linux-based assets.
Advanced AI-powered smart cameras like EufyCam S3 Pro blur the line between security and surveillance. CISOs must assess emerging risks and governance gaps.
Samsung’s Galaxy Book6 Ultra offers potent hardware upgrades for enterprise use. But its adoption raises performance, governance, and supplier trust issues.

New research links specific MITRE techniques to unique cloud alert patterns by threat actors. CISOs can use this for proactive industry-focused defense.
CrowdStrike Falcon delivered 100% detection and protection accuracy in SE Labs’ October 2025 ransomware test, marking four consecutive perfect scores.

Browser extension changes in Manifest v3 broke legacy threat protections. Malwarebytes re-engineered Browser Guard, and CISOs must understand the implications.
The AI-fueled hardware surge is altering upgrade cycles for both gamers and enterprise users. Alienware’s sub-$1,000 laptop deal reflects wider industry shifts.

Budget power stations, often deployed across industrial operations, pose overlooked risks. CISOs must reassess OT expansion safeguards.
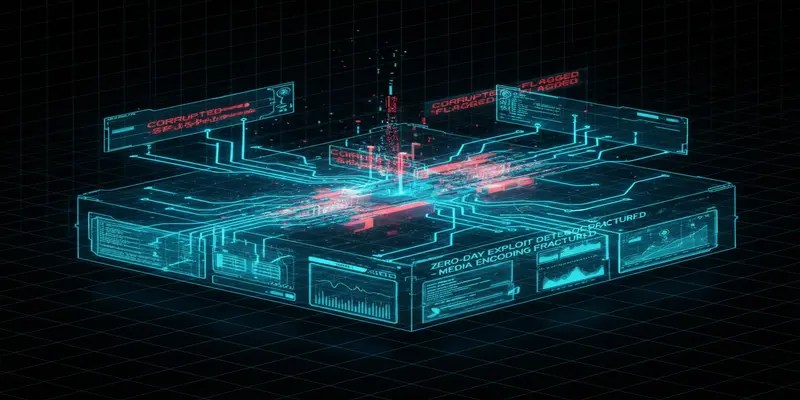
WhatsApp has quietly deployed a Rust-based media handler and new internal file screening to reduce malware-laden file exploits—posing key lessons for mobile defense.

A new cybersecurity report reveals four key issues preventing CISOs from executing a resilient security strategy. From AI governance gaps to talent shortages, here's what security leaders must address now.

Germany's government is signaling a policy shift toward proactive cyber retaliation against foreign adversaries. CISOs should reassess their posture and readiness.

With the proliferation of rechargeable devices in enterprise environments, lithium battery hazards are an overlooked safety and security threat.