
Upwind Choppy AI Revolutionizes Cloud Security Exploration for CISOs
Upwind has introduced Choppy AI, a natural-language interface integrated into its CNAPP platform to simplify cloud security exploration and investigation for security teams.
As organizations accelerate cloud adoption, new attack surfaces emerge across AWS, Azure, Google Cloud, and SaaS platforms. This section covers cloud misconfigurations, container security issues, identity-based attacks, and data exposure incidents in cloud environments.
24 articles

Upwind has introduced Choppy AI, a natural-language interface integrated into its CNAPP platform to simplify cloud security exploration and investigation for security teams.

The ALDO Group transformed its global retail cybersecurity by consolidating defenses on the AI-driven CrowdStrike Falcon platform, enhancing visibility and risk management.

This analysis offers CISOs a deep technical evaluation of Wiz’s AI-powered automated threat detection and response capabilities, comparing it with peers and highlighting actionable insights.

Wiz sets a new standard in CSPM with AI-powered automated threat detection and response. This article guides CISOs in evaluating Wiz’s AI security capabilities effectively.

Wiz built its reputation on agentless cloud visibility. Now it's betting on AI — from automated threat investigation to AI-BOM and AI-SPM. A frank look at what each feature actually does, what it delivers, and where the gaps remain.

Microsoft's latest security enhancements leverage autonomous defense in Defender combined with expert-led services, enabling CISOs to scale operations and improve threat response efficiency.
Wiz has released a groundbreaking benchmark suite to evaluate AI agents in real-world cybersecurity scenarios. Claude Code on Opus 4.6 currently leads.

New research links specific MITRE techniques to unique cloud alert patterns by threat actors. CISOs can use this for proactive industry-focused defense.
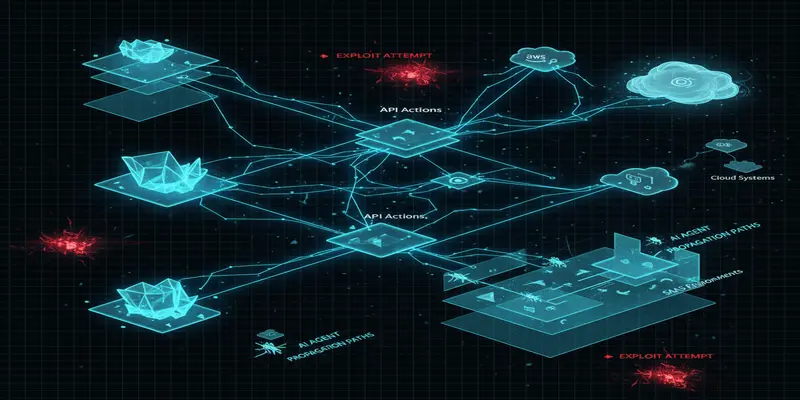
AI agents are creating dynamic new risks across enterprise environments. Microsoft’s latest insights highlight where CISOs must adapt defenses for real-time protection.
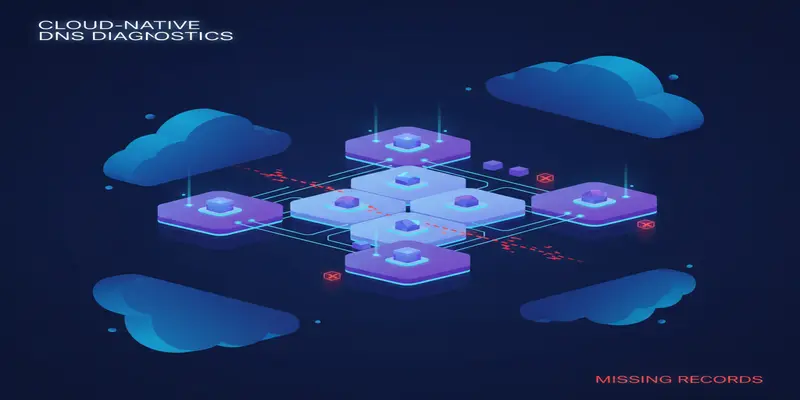
A logic flaw in Azure Private Link DNS behavior can unintentionally block access to resources, creating stealthy DoS attacks. We unpack the implications and fixes.
Browse the latest cybersecurity incidents and threat intelligence by topic.
Threat intelligence is the foundation of proactive cybersecurity defense.
View ArticlesArtificial intelligence is reshaping both offensive and defensive cybersecurity.
View ArticlesPhishing remains the most common initial access vector in cyber attacks.
View ArticlesRansomware attacks continue to be one of the most disruptive cyber threats facing organizations worldwide.
View ArticlesZero-day vulnerabilities represent the most dangerous class of security flaws because no patches exist at the time of discovery.
View ArticlesData breaches expose sensitive information and erode customer trust.
View ArticlesMalware continues to evolve with increasingly sophisticated evasion techniques and delivery mechanisms.
View ArticlesEffective vulnerability management is critical for reducing organizational risk.
View Articles