Zombie ZIP Method Can Evade Antivirus Detection on Initial Scan: What CISOs Need to Know
The Zombie ZIP technique tricks antivirus scanners by falsifying ZIP headers, evading initial malware detection. CISOs must update defenses with this insight.
Malware continues to evolve with increasingly sophisticated evasion techniques and delivery mechanisms. This section analyzes new malware families, infection chains, command-and-control infrastructure, and defensive measures for enterprise environments.
13 articles
The Zombie ZIP technique tricks antivirus scanners by falsifying ZIP headers, evading initial malware detection. CISOs must update defenses with this insight.

This analysis details leading antivirus software for 2026, emphasizing features relevant to CISOs managing enterprise security. It offers guidance on selecting solutions amid evolving cyber threats.
Over 1,200 on-premises IceWarp servers remain exposed to a critical unauthenticated OS command injection vulnerability (CVE-2025-14500). Immediate remediation is imperative for CISOs.

This cybersecurity report evaluates the top antivirus solutions of 2026, highlighting their relevance and effectiveness for enterprise security leaders.
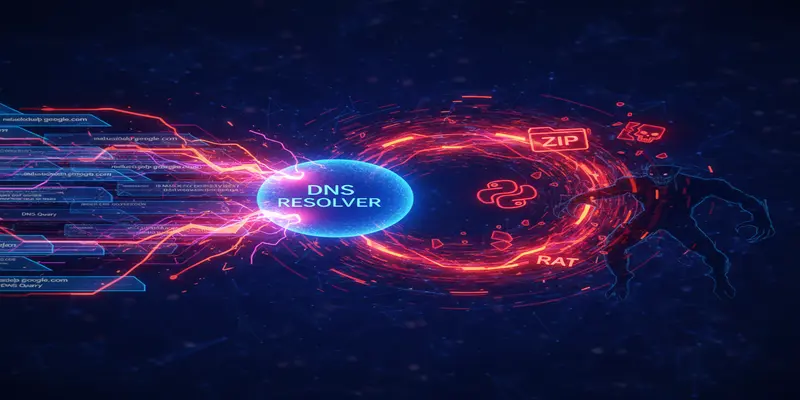
ClickFix campaigns now exploit the nslookup utility to deliver payloads hidden in DNS responses, bypassing traditional PowerShell defenses.

VoidLink, a modular Linux malware framework, is being used by UAT-9921. CISOs should assess visibility and controls around cloud and hybrid Linux-based assets.
WhatsApp has quietly deployed a Rust-based media handler and new internal file screening to reduce malware-laden file exploits—posing key lessons for mobile defense.
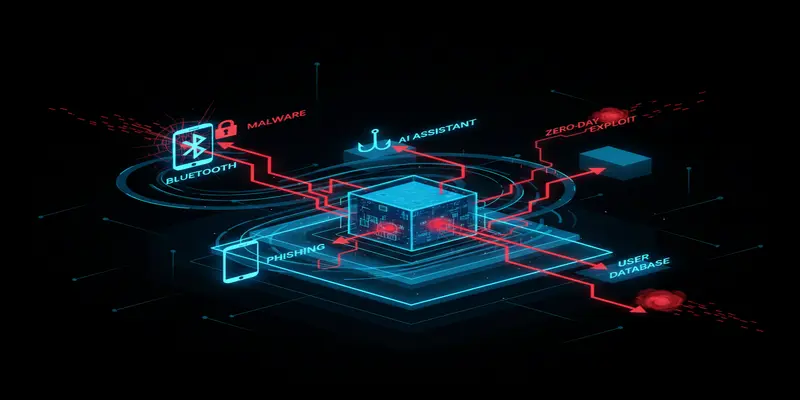
Malwarebytes’ latest roundup showcases an escalating threat landscape involving Bluetooth exploits, phishing on LinkedIn, and hidden remote backdoors.

A sophisticated fake WinRAR campaign hides malware behind a genuine-looking installer. CISOs must assess exposure to malicious file download vectors.

A ferry in Italy was compromised by IoT malware likely deployed by someone physically onboard. This unusual breach reveals critical security blind spots in maritime and operational technology.
Browse the latest cybersecurity incidents and threat intelligence by topic.
Threat intelligence is the foundation of proactive cybersecurity defense.
View ArticlesArtificial intelligence is reshaping both offensive and defensive cybersecurity.
View ArticlesPhishing remains the most common initial access vector in cyber attacks.
View ArticlesRansomware attacks continue to be one of the most disruptive cyber threats facing organizations worldwide.
View ArticlesZero-day vulnerabilities represent the most dangerous class of security flaws because no patches exist at the time of discovery.
View ArticlesAs organizations accelerate cloud adoption, new attack surfaces emerge across AWS, Azure, Google Cloud, and SaaS platforms.
View ArticlesData breaches expose sensitive information and erode customer trust.
View ArticlesEffective vulnerability management is critical for reducing organizational risk.
View Articles