
Framework Laptop 13 Pro Emerges as a Modular Windows Security Game-Changer
Framework’s Laptop 13 Pro, nicknamed the “MacBook Pro for Linux users,” pushes modular Windows laptop innovation, challenging enterprise security paradigms.
Supply chain attacks compromise trusted software and hardware to infiltrate downstream targets. This section tracks supply chain compromises, dependency hijacking, and third-party risk incidents that affect enterprise security postures.
20 articles

Framework’s Laptop 13 Pro, nicknamed the “MacBook Pro for Linux users,” pushes modular Windows laptop innovation, challenging enterprise security paradigms.

This cybersecurity report explores how CISOs can seize major sales events to upgrade critical IT assets, balancing cost and security to strengthen organizational resilience.
Malwarebytes introduces File Shredder to securely and irreversibly delete sensitive files on Windows devices. CISOs gain control over data disposition with this tool.

The Stargear 3-in-1 cable significantly improves power flexibility for Starlink Mini users, including off-grid and mobile deployments critical for secure network resilience.

Recent analysis exposes vulnerabilities in popular password managers that allow data theft through server control. CISOs must understand these risks to protect enterprise vaults and credentials.

This analysis explores leveraging green energy-style tax incentives and digital trust labels to strengthen cybersecurity accountability and protect data assets. CISOs should evaluate these evolving policy incentives for future strategy.
The Acer Swift Edge 14’s use of last-gen hardware raises questions for CISOs managing device lifecycles in 2026. Explore risk exposure and strategy.
Samsung’s Galaxy Book6 Ultra offers potent hardware upgrades for enterprise use. But its adoption raises performance, governance, and supplier trust issues.
The Clawdbot agent is gaining popularity for automating tasks, but hides significant cyber risk. CISOs must assess the implications of exposing systems to unsecured AI.
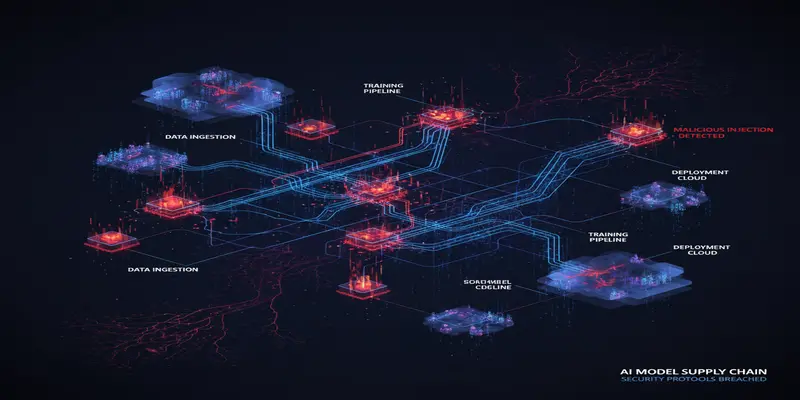
Microsoft researchers uncovered attacker-manipulated AI models with embedded backdoors, posing serious supply chain risks. CISOs must act now.
Browse the latest cybersecurity incidents and threat intelligence by topic.
Threat intelligence is the foundation of proactive cybersecurity defense.
View ArticlesArtificial intelligence is reshaping both offensive and defensive cybersecurity.
View ArticlesPhishing remains the most common initial access vector in cyber attacks.
View ArticlesRansomware attacks continue to be one of the most disruptive cyber threats facing organizations worldwide.
View ArticlesZero-day vulnerabilities represent the most dangerous class of security flaws because no patches exist at the time of discovery.
View ArticlesAs organizations accelerate cloud adoption, new attack surfaces emerge across AWS, Azure, Google Cloud, and SaaS platforms.
View ArticlesData breaches expose sensitive information and erode customer trust.
View ArticlesMalware continues to evolve with increasingly sophisticated evasion techniques and delivery mechanisms.
View Articles