Zombie ZIP Method Can Evade Antivirus Detection on Initial Scan: What CISOs Need to Know
The Zombie ZIP technique tricks antivirus scanners by falsifying ZIP headers, evading initial malware detection. CISOs must update defenses with this insight.
Threat intelligence is the foundation of proactive cybersecurity defense. This section covers the latest threat actor campaigns, indicators of compromise, and intelligence reports that help security teams anticipate and mitigate attacks before they cause damage.
38 articles
The Zombie ZIP technique tricks antivirus scanners by falsifying ZIP headers, evading initial malware detection. CISOs must update defenses with this insight.

Agentic AI’s rise brings transformative capabilities alongside significant security challenges that CISOs must prioritize to safeguard their organizations.

Ransomware attacks continue to rise with sophisticated tactics and diverse threat actors. CISOs must understand these top 15 active ransomware groups to bolster defenses effectively.

Cisco Talos monitors limited cyber incidents amid the Middle East conflict, urging CISOs to strengthen defenses against regional hacktivism and threat actor activity.

The Stargear 3-in-1 cable significantly improves power flexibility for Starlink Mini users, including off-grid and mobile deployments critical for secure network resilience.

Microsoft's latest security enhancements leverage autonomous defense in Defender combined with expert-led services, enabling CISOs to scale operations and improve threat response efficiency.

Japanese-language phishing emails targeting Japanese speakers are leveraging .cn domains and brand impersonation, raising significant risks for enterprise email security.

Microsoft has released a new e-book on Security Exposure Management that empowers CISOs to adopt proactive defense strategies. The guide highlights best practices for reducing security risks effectively.

Chrome’s preloading feature, designed to enhance browsing speed, can inadvertently expose enterprise data and trigger security tools, raising concerns for CISOs about operational risks and privacy.
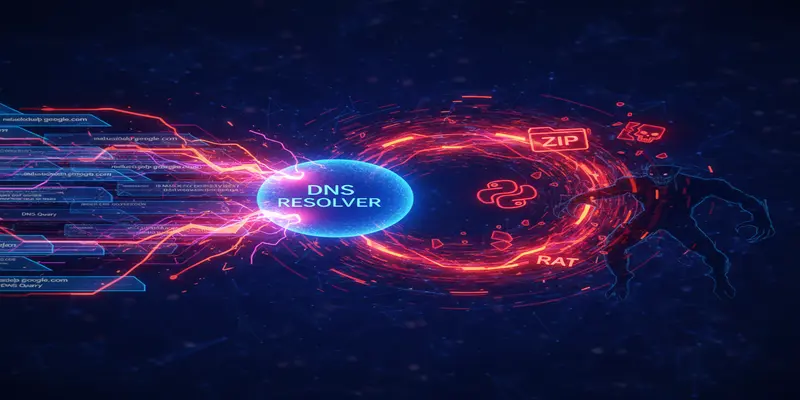
ClickFix campaigns now exploit the nslookup utility to deliver payloads hidden in DNS responses, bypassing traditional PowerShell defenses.
Browse the latest cybersecurity incidents and threat intelligence by topic.
Artificial intelligence is reshaping both offensive and defensive cybersecurity.
View ArticlesPhishing remains the most common initial access vector in cyber attacks.
View ArticlesRansomware attacks continue to be one of the most disruptive cyber threats facing organizations worldwide.
View ArticlesZero-day vulnerabilities represent the most dangerous class of security flaws because no patches exist at the time of discovery.
View ArticlesAs organizations accelerate cloud adoption, new attack surfaces emerge across AWS, Azure, Google Cloud, and SaaS platforms.
View ArticlesData breaches expose sensitive information and erode customer trust.
View ArticlesMalware continues to evolve with increasingly sophisticated evasion techniques and delivery mechanisms.
View ArticlesEffective vulnerability management is critical for reducing organizational risk.
View Articles