AI Agents Compete in Security Tests as Wiz Sets New Benchmark
Wiz has released a groundbreaking benchmark suite to evaluate AI agents in real-world cybersecurity scenarios. Claude Code on Opus 4.6 currently leads.
Artificial intelligence is reshaping both offensive and defensive cybersecurity. This section tracks AI-driven threats including prompt injection, model poisoning, adversarial machine learning, and vulnerabilities in large language models used across enterprise environments.
38 articles
Wiz has released a groundbreaking benchmark suite to evaluate AI agents in real-world cybersecurity scenarios. Claude Code on Opus 4.6 currently leads.

VoidLink, a modular Linux malware framework, is being used by UAT-9921. CISOs should assess visibility and controls around cloud and hybrid Linux-based assets.

A new Microsoft study reveals how a single adversarial prompt can fully bypass the safety alignment of large language models. CISOs must assess AI risk posture.
Advanced AI-powered smart cameras like EufyCam S3 Pro blur the line between security and surveillance. CISOs must assess emerging risks and governance gaps.
The Clawdbot agent is gaining popularity for automating tasks, but hides significant cyber risk. CISOs must assess the implications of exposing systems to unsecured AI.
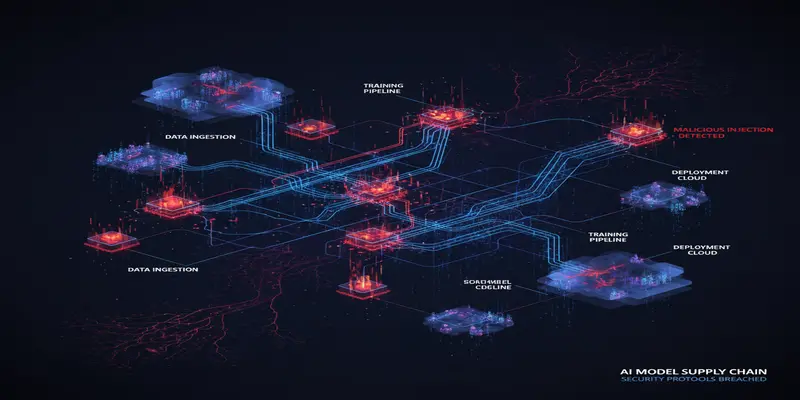
Microsoft researchers uncovered attacker-manipulated AI models with embedded backdoors, posing serious supply chain risks. CISOs must act now.
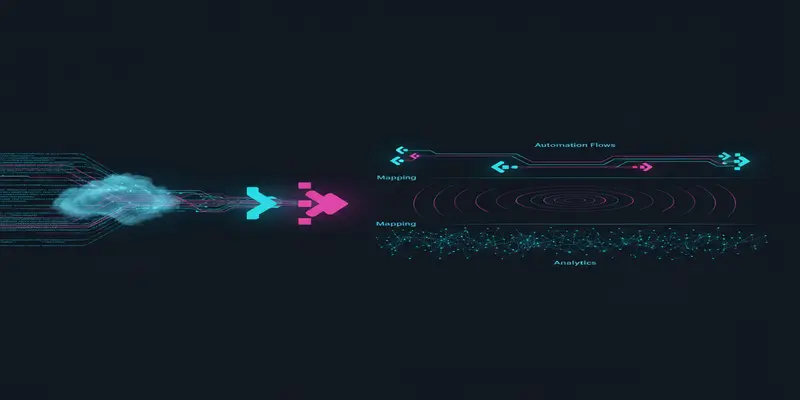
Microsoft is using generative AI to turn raw threat reports into immediately actionable detection rules. CISOs must adapt their detection lifecycle strategy.

A new cybersecurity report reveals four key issues preventing CISOs from executing a resilient security strategy. From AI governance gaps to talent shortages, here's what security leaders must address now.

AI is driving a seismic shift in the 2026 cyber threat landscape. This threat intelligence report outlines critical risks, attacker methods, and mitigation paths.
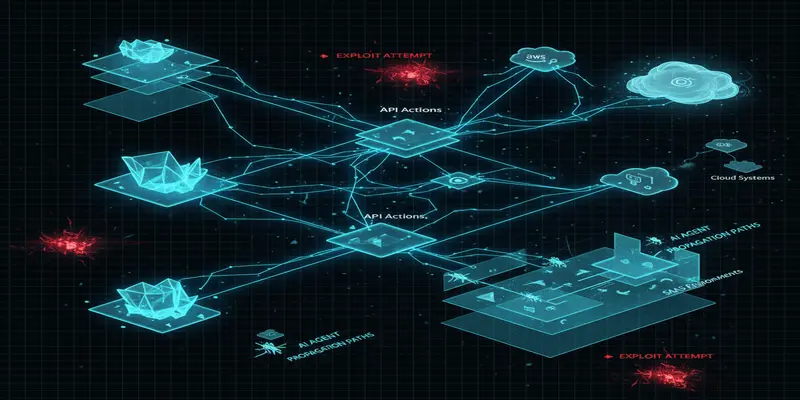
AI agents are creating dynamic new risks across enterprise environments. Microsoft’s latest insights highlight where CISOs must adapt defenses for real-time protection.
Browse the latest cybersecurity incidents and threat intelligence by topic.
Threat intelligence is the foundation of proactive cybersecurity defense.
View ArticlesPhishing remains the most common initial access vector in cyber attacks.
View ArticlesRansomware attacks continue to be one of the most disruptive cyber threats facing organizations worldwide.
View ArticlesZero-day vulnerabilities represent the most dangerous class of security flaws because no patches exist at the time of discovery.
View ArticlesAs organizations accelerate cloud adoption, new attack surfaces emerge across AWS, Azure, Google Cloud, and SaaS platforms.
View ArticlesData breaches expose sensitive information and erode customer trust.
View ArticlesMalware continues to evolve with increasingly sophisticated evasion techniques and delivery mechanisms.
View ArticlesEffective vulnerability management is critical for reducing organizational risk.
View Articles